| Industrial automation devices typically need to communicate using protocols such as PROFINET, PROFIBUS, EtherNet/IP or EtherCAT. Join our li...
More about Cyber Security (32)
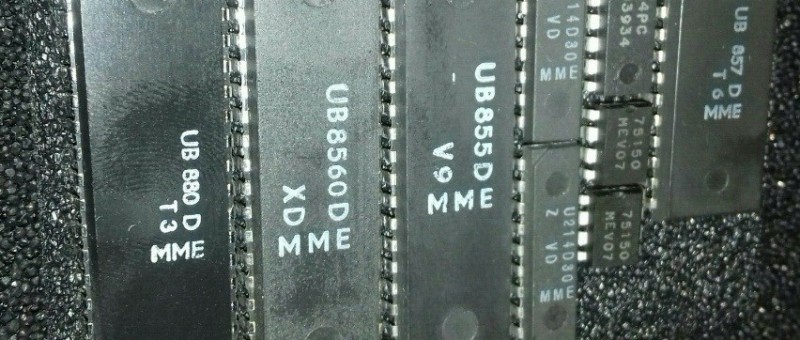
| Detect USB Kill flash drives before they harm your hardware.
| Interested in espionage and security? Join the Elektor Spy Contest! Read carefully through Luka Matic's book and try to find better answers...
| Looking for a good book to get you through Christmas? How about the “Handbook on DIY Electronic Security and Espionage”? Learn all the trick...
| If you are interested in espionage and security, you may like to participate in our Spy Contest! Analyze my book, find (better) answers/solu...
| [Partner Content] The new platform enables manufacturers and operators to ensure network equipment supports massive data volumes and cyberse...
| The COVID-19 crisis continues to unfold, we are monitoring the electronics industry and posting about important news. This week, we update y...
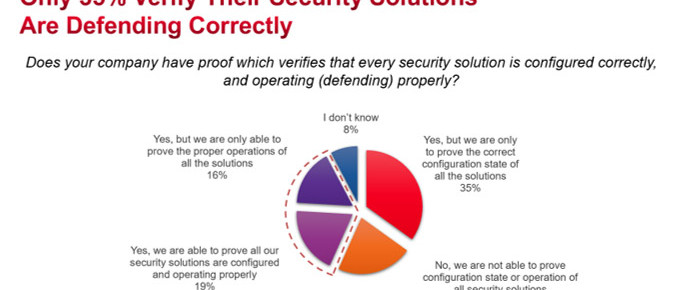
| This is a submission from Keysight Technologies on their Security Operations Effectiveness survey. It shows that security professionals are...
| This is a submission from Keysight Technologies. They have joined the Orbital Security Alliance (OSA) as a full member. The OSA was founded...
| The Internet of Things (IoT) will see connectivity applied on a far bigger scale than anything we have seen before. With the prospect of ten...