Brain-Machine Interfaces Threaten Privacy of Thought
on
Brain-computer interfaces (BCIs) are gaining popularity as prices drop and the technology develops. The gaming industry, always ahead of the curve when it comes to innovative interfaces, already embraces the devices as game-controllers. The multiplayer online game Throw Trucks With Your Mind measures brain activity with an affordable EEG-headset to integrate parameters like focus and calm into the game.
But hooking up your brain to a computer linked to the internet –although extremely fascinating- unfortunately also has its disadvantages. A team of researchers from the University of Oxford, UC Berkeley and the University of Geneva are the first to examine the security risks involved in using such technology. From a series of experiments they concluded it is possible to collect private and secret information from unsuspecting users. Their findings were published in the paper On the Feasibility of Side-Channel Attacks with Brain-Computer Interfaces (link below).
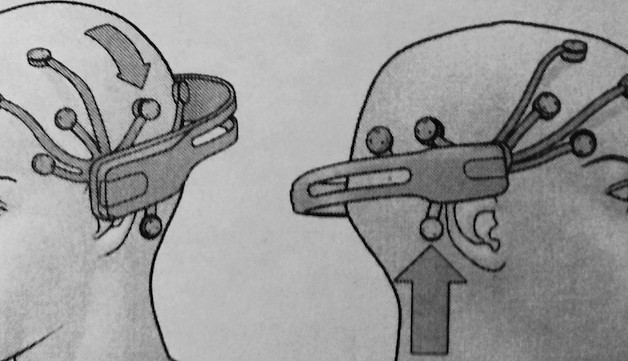
In order to recreate a realistic test environment the researchers used the EPOC neuroheadset made available to the consumer market by the company Emotiv Systems. The EPOC, like most BCIs, uses EEG (electroencephalography) to measure brain wave patterns by recording the electrical fields produced by neuron activity.
For their research the team made use of a phenomenon that shows up on EEG read-outs called event-related-potential (ERP). An ERP is a change in the voltage pattern a short time-interval after the subject is presented with a certain stimulus. For instance, when a person is shown a series of pictures of people she doesn’t know the EEG-signal stays fairly constant but when a familiar face flashes by there is an amplitude peak 300 milliseconds after the event.
In theory ERPs can reveal secret knowledge of the user to an attacker who is in the position to ask the right questions. To test the hypothesis the team set up an experiment where 30 students were asked to wear the EPOC while watching a computer screen. In one test they were asked which month they were born and then names of the months were randomly shown on the screenIn another test designed to filch the PIN code of the subjects no questions were asked but numbers were randomly presented to them.
The results of the tests varied. The success rate of data extraction was measured against a random guess attack. Attacks using the EEG data were 10 to 40 percent more successful than random guesses. That may seem modest but BCI technology is still in the early stages of its development cycle and is expected to improve significantly.
The experimental set-up the researchers used in which they were in the position to pose questions to the users can also be found in the wild. Companies selling neuroheadsets like Emotiv and its competitor Neurosky allow third parties to develop applications for their products. That is understandable since the EPOC wouldn’t be much fun if there weren’t games available to use it on. But developers have full access to the EEG data and the applications have complete control over the stimuli presented to the user. Both conditions are necessary to develop applications like Throw Trucks With Your Mind. But in the hands of a malicious developer it could lead to dark scenario’s.
Ryan Calo, an academic who combines his law degree with an expertise in emerging technologies, advises brain app stores should be heavily curated to prevent brain spyware from being released. He also points out that the technology might be to good for overzealous law enforcements agencies to resist. He gives the example of an Amber alert in which the picture of a missing child is distributed online. BCI wearing gamers could find themselves on the suspects list based merely on their brain response.
On the Feasibility of Side-Channel Attacks with Brain-Computer Interfaces (link to PDF at the bottom of that page).
Images: Drawing: Mynameiskavi, ERP graph: Neurofeedback.visaduma.info


Discussion (1 comment)