USB cable: espionage, sabotage, infiltration
on
 What do you do when you’ve misplaced or forgotten your USB cable, the one you use every day to charge your phone? You borrow another one, of course, and you’re good to go. And you don’t worry about the unpleasant consequences that this simple loan might have… In fact, for most people, part of the vulnerability of the USB interface often goes completely unnoticed.
What do you do when you’ve misplaced or forgotten your USB cable, the one you use every day to charge your phone? You borrow another one, of course, and you’re good to go. And you don’t worry about the unpleasant consequences that this simple loan might have… In fact, for most people, part of the vulnerability of the USB interface often goes completely unnoticed.
Spy microcontroller hidden in the connector
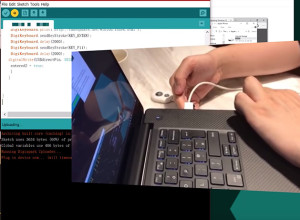
We’ve certainly learned to beware of USB memory sticks, but our vigilance stops there. Nonetheless, if this subject interests you, you are doubtless aware that inside the USB connector it is possible to conceal a microcontroller. That is capable of transforming a common-looking USB cable into a formidable hacking tool. A few years ago, when this possibility (often called BadUSB) was brought to light, it made a bit of noise. It has been made practical in an interesting product (but one of debatable uses!)The microcontroller hidden in the connector of the USB Ninja cable is notable in that it communicates wirelessly with the outside world. It is its Bluetooth interface which allows the person controlling the USB Ninja to surreptitiously load malware or spyware.
Programming the device can be done directly in C or in the Arduino programming environment (IDE). Unlocking the device is done with the aid of a small magnet.


Discussion (1 comment)