| Secure communication is essential in modern embedded systems, particularly in distributed and IoT applications. This article presents a prac...
More about Cryptography (39)
| From Caesar ciphers to AES and RSA on real boards, Practical Microcontroller Cryptography shows how cryptography actually runs on microcontr...
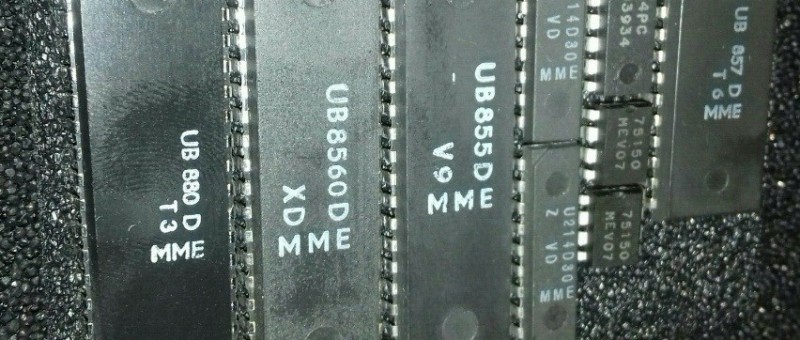
| Hardware Security Modules (HSMs) are electronic devices using various hardware protection schemes against unauthorized reading of the secret...
| Analog Devices (ADI) is one of the world’s major designers and manufacturers of analog, mixed-signal, and digital signal processing integrat...
| Interested in espionage and security? Join the Elektor Spy Contest! Read carefully through Luka Matic's book and try to find better answers...
| Looking for a good book to get you through Christmas? How about the “Handbook on DIY Electronic Security and Espionage”? Learn all the trick...
| Microchip University’s Cryptography Primer course targets those unfamiliar with how cryptography works or those very rusty and in need of a...
| If you are interested in espionage and security, you may like to participate in our Spy Contest! Analyze my book, find (better) answers/solu...
| Join Microchip and Elektor for the webinar "Cryptography Primer" to learn about the fundamentals of cryptography. Both symmetric and asymmet...
| This is a submission from Microchip on its CryptoAutomotive™ security IC, the TrustAnchor100. The cryptographic companion device supports in...