Congatec significantly lowers the price threshold for 64bit x86 computing
February 11, 2016
on
on
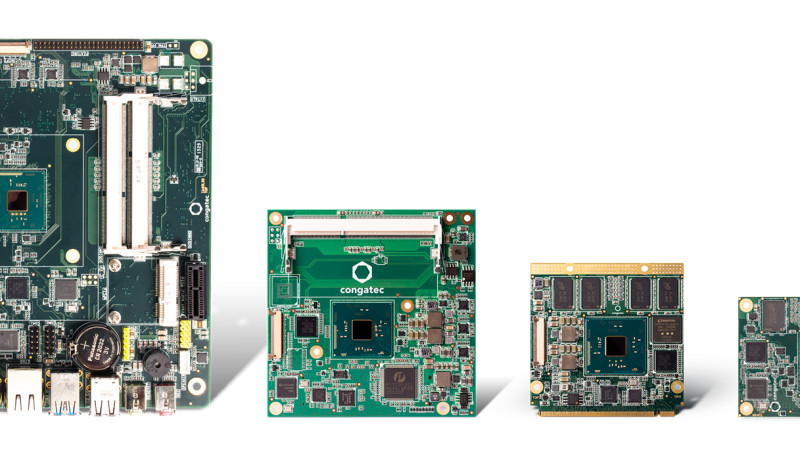
Congatec has introduced new and highly cost-effective versions of its existing COM Express and Qseven modules as well as Mini-ITX boards. They are all equipped with the strategically low-priced, long-term available Intel® Atom™ x5-E8000 processor. This 64bit quadcore processor significantly lowers the entry threshold of powerful x86 computing and, now also in terms of price, offers developers a true alternative to competing platforms based on ARM technology.
“Our new Mini-ITX boards and COM Express and Qseven modules open up new perspectives to developers: The Intel® Atom™ x5-E8000 processor with a 7 year availability brings us into price regions for 64bit x86 processors which compete with corresponding quadcore ARM processors. At the same time, developers can stay in their familiar and proven x86 ecosystem which has evolved over decades and thus they can achieve enormous gains in design efficiency,“ Martin Danzer, director product management at congatec, explains.
Target applications of the new price-breaking embedded computers for x86 technology are very diverse and range from all kinds of embedded mobile devices, industrial gateways, terminal, ticket and cash register systems in the retail segment right up to gaming machines and digital signage systems. Other fields of application can also be found in compact industrial PCs as well as in medical devices and systems in the transport sector.
Thanks to its integrated quadcore SoC, with a processor TDP of 5 watts and a SDP of just 4 watts, the congatec boards and modules with Intel® Atom™ x5-E8000 processor deliver high multi-thread performance for applications in the lower performance segment. This plays an important role, for example, in IoT applications, which have to execute an array of additional tasks alongside their actual application such as de- and encrypting, virus protection and network traffic.
“Our new Mini-ITX boards and COM Express and Qseven modules open up new perspectives to developers: The Intel® Atom™ x5-E8000 processor with a 7 year availability brings us into price regions for 64bit x86 processors which compete with corresponding quadcore ARM processors. At the same time, developers can stay in their familiar and proven x86 ecosystem which has evolved over decades and thus they can achieve enormous gains in design efficiency,“ Martin Danzer, director product management at congatec, explains.
Target applications of the new price-breaking embedded computers for x86 technology are very diverse and range from all kinds of embedded mobile devices, industrial gateways, terminal, ticket and cash register systems in the retail segment right up to gaming machines and digital signage systems. Other fields of application can also be found in compact industrial PCs as well as in medical devices and systems in the transport sector.
Thanks to its integrated quadcore SoC, with a processor TDP of 5 watts and a SDP of just 4 watts, the congatec boards and modules with Intel® Atom™ x5-E8000 processor deliver high multi-thread performance for applications in the lower performance segment. This plays an important role, for example, in IoT applications, which have to execute an array of additional tasks alongside their actual application such as de- and encrypting, virus protection and network traffic.
Read full article
Hide full article


Discussion (0 comments)