| How can a modern SSO authentication solution increase computer and network security and reduce cyber risks? ELATEC's white paper explains wh...
More about secure (17)
| Interested in espionage and security? Join the Elektor Spy Contest! Read carefully through Luka Matic's book and try to find better answers...
| Looking for a good book to get you through Christmas? How about the “Handbook on DIY Electronic Security and Espionage”? Learn all the trick...
| If you are interested in espionage and security, you may like to participate in our Spy Contest! Analyze my book, find (better) answers/solu...
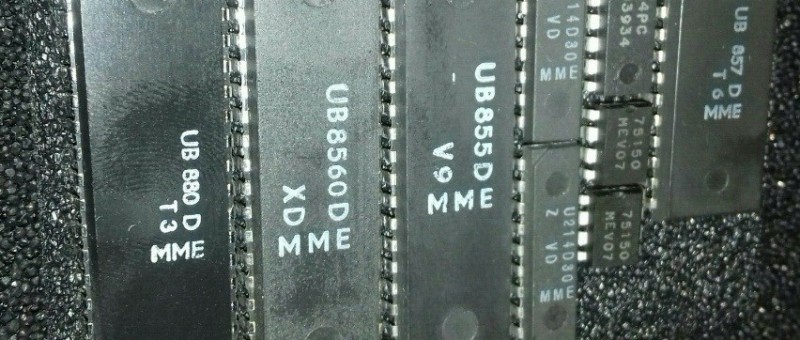
| This is a submission from Apacer on a series of rugged industrial SSDs, which uses industrial-grade wide-temperature ICs sourced directly fr...
| SD cards are small, cheap, lightweight, and fast, and they can hold many gigabytes of data. However, because of their physical properties, t...
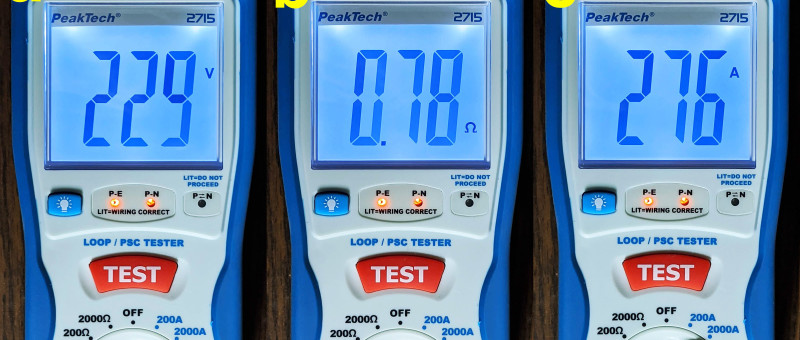
| Looking for a digital loop/PSC tester? The PeakTech 2715 is a handy test device that enables electricians and DIYers alike to check whether...
| In a recently released preliminary report by the US House Transportation Committee criticism is levelled not only at Boeing for engineering...
| Alice likes to keep her conversations with Bob private. Secure communication schemes are necessary to hide information from Eavesdropping Ev...
| Mobile devices such as smartphones are currently protected from improper use by a password, swipe gesture and fingerprint or face recognitio...