| Winbond W77Q delivers robust firmware protection for embedded developers — NIST-compliant, PQC-ready, and easy to drop into existing designs...
More about Security (158)
| Firmware updates for IoT devices close security gaps, add features, and extend system life. However, insecure updates pose risks. This artic...
| From smart factories to secure workplaces, seamless access control is essential. ELATEC TWN4 universal RFID readers support virtually any RF...
| [Partner Content] Microchip has announced the release of version 2.4 of the TimeProvider® 4100 grandmaster firmware with an embedded BlueSky...
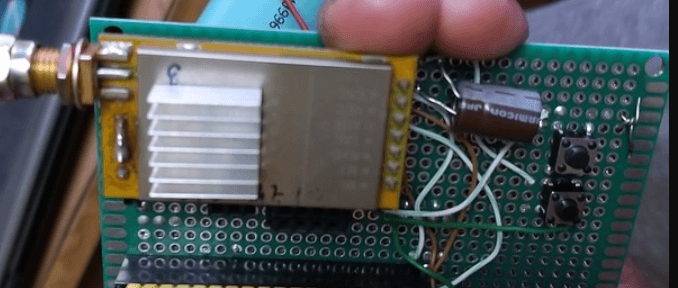
| Let's make a homemade wireless ESP32-CAM WiFi Surveillance Camera using an ESP32-CAM module.
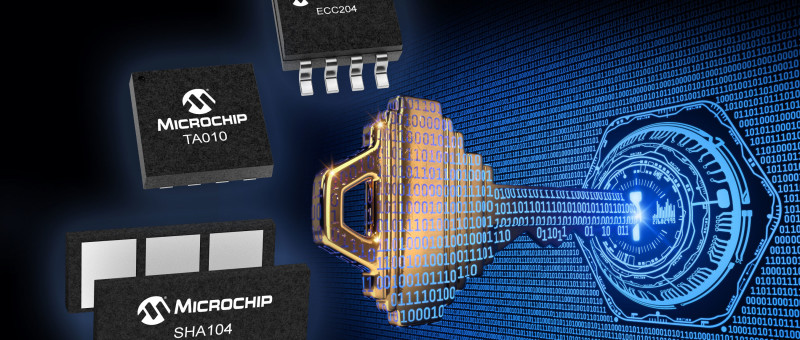
| [Partner Content] To defend against current and ever-expanding security threats, Microchip Technology has launched the PIC18-Q24 Family of M...
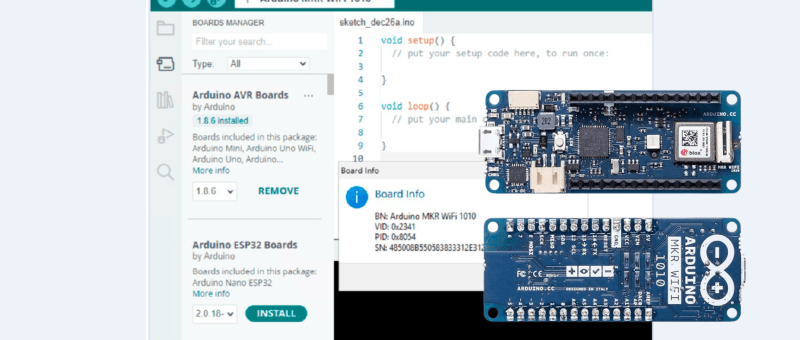
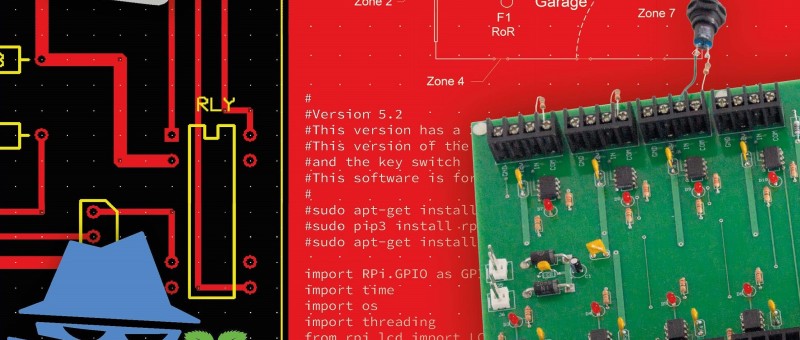
| An innovative engineer can solve a problem in a complicated industrial environment with a few low-cost electronic modules and some Arduino p...
| A car drives up to the closed gate, where a high-resolution camera reads its license plate. If it exists in the gatekeeper’s database, the g...
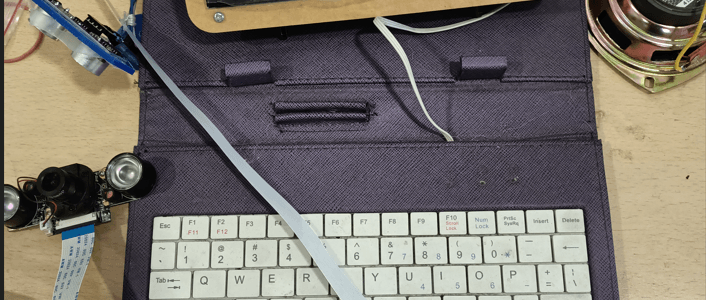
| Have you seen the movie "Mission Impossible” with Tom Cruise? Would you like to know how to catch him with a $40 sensor? Try building a high...
| [Partner Content] Six new security-focused products aim to optimize and scale embedded security across a wide range of industries including...